Contact enrichment for sourcing
Finding and verifying contact details, primarily work email addresses, for passive candidates already identified through sourcing, so outreach can reach them directly without guessing.
Michal Juhas · Last reviewed May 4, 2026
What is contact enrichment for sourcing?
Contact enrichment for sourcing means finding a verified way to reach passive candidates you have already identified. You have the name and the LinkedIn profile; enrichment adds the work email or phone number that lets your message actually arrive. Done without verification or consent records, it drains deliverability and creates compliance exposure before the first reply comes in.
In practice
- A sourcer builds a Boolean string on LinkedIn, saves a shortlist of 50 profiles, then runs the export through an enrichment tool to find verified work emails before loading into an outreach sequence. The "reveal" button in most sourcing tools is a single-click version of this flow.
- A recruiting ops lead saying "our hit rate from Apollo is dropping" means the share of sourced profiles that return a verified email has fallen below the pipeline target, often because people have changed jobs or employers have switched email domains.
- GDPR notices from candidates that read "you found my contact details from a third party" almost always point to an enrichment vendor, which is why vendor names belong in your privacy notice and DPA documentation, not just a procurement spreadsheet.
Quick read, then how hiring teams use it
This is for recruiters, sourcers, TA, and HR partners who need the same vocabulary in debriefs, vendor calls, and policy reviews. Skim the first section when you need a fast shared picture. Use the second when you are deciding how it shows up in the ATS, sourcing tools, or candidate communications.
Plain-language summary
- What it means for you: You found the right person on LinkedIn but have no direct way to message them. Contact enrichment gives you a work email so your outreach arrives instead of disappearing into a connection request pile.
- How you would use it: You export sourced profiles, run them through a lookup tool, verify the results, and load the clean list into your outreach sequence.
- How to get started: Pick one lookup provider and one verification tool. Run ten profiles of people you already hired to see how accurate the output is before you touch a live campaign.
- When it is a good time: After sourcing criteria are stable and legal has reviewed your vendor DPAs. Not while your Boolean strings are still changing every Monday.
When you are running live reqs and tools
- What it means for you: Enrichment moves personal data between systems, so GDPR, retention schedules, and vendor subprocessors matter as much as match rates. Pair with workflow automation hygiene so the data pipeline is auditable, not just fast.
- When it is a good time: When your sourcing pipeline is stable, CRM hygiene is blocking campaigns, or hiring managers need direct contact for specialised roles where LinkedIn InMail response rates are too low.
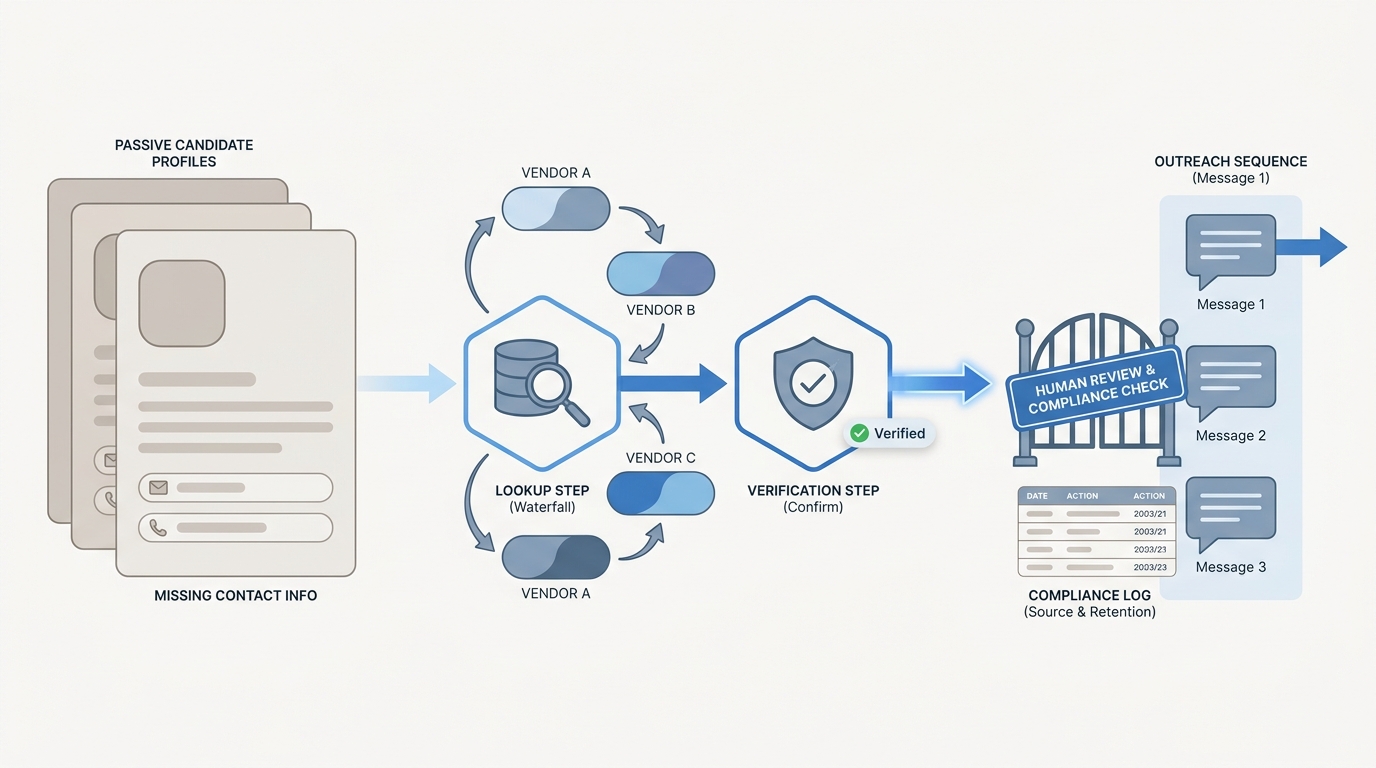
- How to use it: Build a waterfall of two or three providers, verify every output before sequence import, log source and verification date per row, and keep a human review queue for low-confidence results. Read AI sourcing tools for recruiters before you chain vendors.
- How to get started: Pilot on an alumni or warm-contact list where consent is clearer, then move to net-new passive sourcing once the workflow is stable and error rates are flat for a few weeks.
- What to watch for: Hard bounce spikes above two percent, duplicate rows in the ATS from multiple enrichment runs, models guessing emails that fail verification, and vendors that do not offer EU data residency when you need it.
Where we talk about this
On AI with Michal live sessions, sourcing automation blocks treat contact enrichment as the moment personal data leaves one API and lands in another: keys, logs, and failure alerts get real fast. AI in recruiting blocks connect the same flows back to GDPR and hiring manager trust. Bring your vendor contracts and a sample export to Workshops if you want practical pressure-testing alongside peers, not just theory on a slide.
Around the web (opinions and rabbit holes)
Third-party creators move fast. Treat these as starting points, not endorsements, and double-check anything before you wire candidate data.
YouTube
- Clay tutorial: waterfall enrichment for outreach (Clay) covers multi-provider lookup cascades that translate directly to sourcing use cases.
- How to find anyone's email for recruiting outreach (Patrick Dang) walks the finder-then-verify pattern sourcers use before wiring sequences.
- Email deliverability masterclass (Lemlist) covers sender reputation, bounce thresholds, and warmup in terms that apply directly to sourcing outreach.
- Best tool for finding verified emails of candidates? in r/sourcing compares provider accuracy with blunt real-world numbers from people running sequences.
- Anyone using Clay for recruiting or sourcing? in r/recruiting is a frank thread on how sales enrichment tools translate to TA workflows.
- GDPR and cold email outreach to candidates in r/Recruitment covers the compliance angle that vendor demos typically skip.
Quora
- How do recruiters find email addresses for passive candidates? collects practitioner answers on finder tools, verification steps, and consent, though quality varies widely.
Lookup versus verification
| Layer | What it does | When it matters |
|---|---|---|
| Lookup | Finds an email address from name and employer | Start of the pipeline |
| Verification | Confirms the address is live and deliverable | Before sequence import |
| Waterfall | Chains providers to raise hit rate | When one vendor misses |
| Log source | Records which vendor found each field | For GDPR audit trails |
Related on this site
- Glossary: Candidate data enrichment, Workflow automation, Human-in-the-loop (HITL), Hallucination, Multi-channel talent sourcing, Boolean search
- Blog: AI sourcing tools for recruiters, Boolean search vs AI sourcing
- Guides: Sourcers
- Live cohort: Workshops
- Membership: Become a member
